On 2024-06-23, 00:19 AM UTC, a phishing e mail was despatched out to 35,794 e mail addresses by [email protected] with the next content material
Customers who clicked the hyperlink within the e mail have been despatched to a malicious web site:
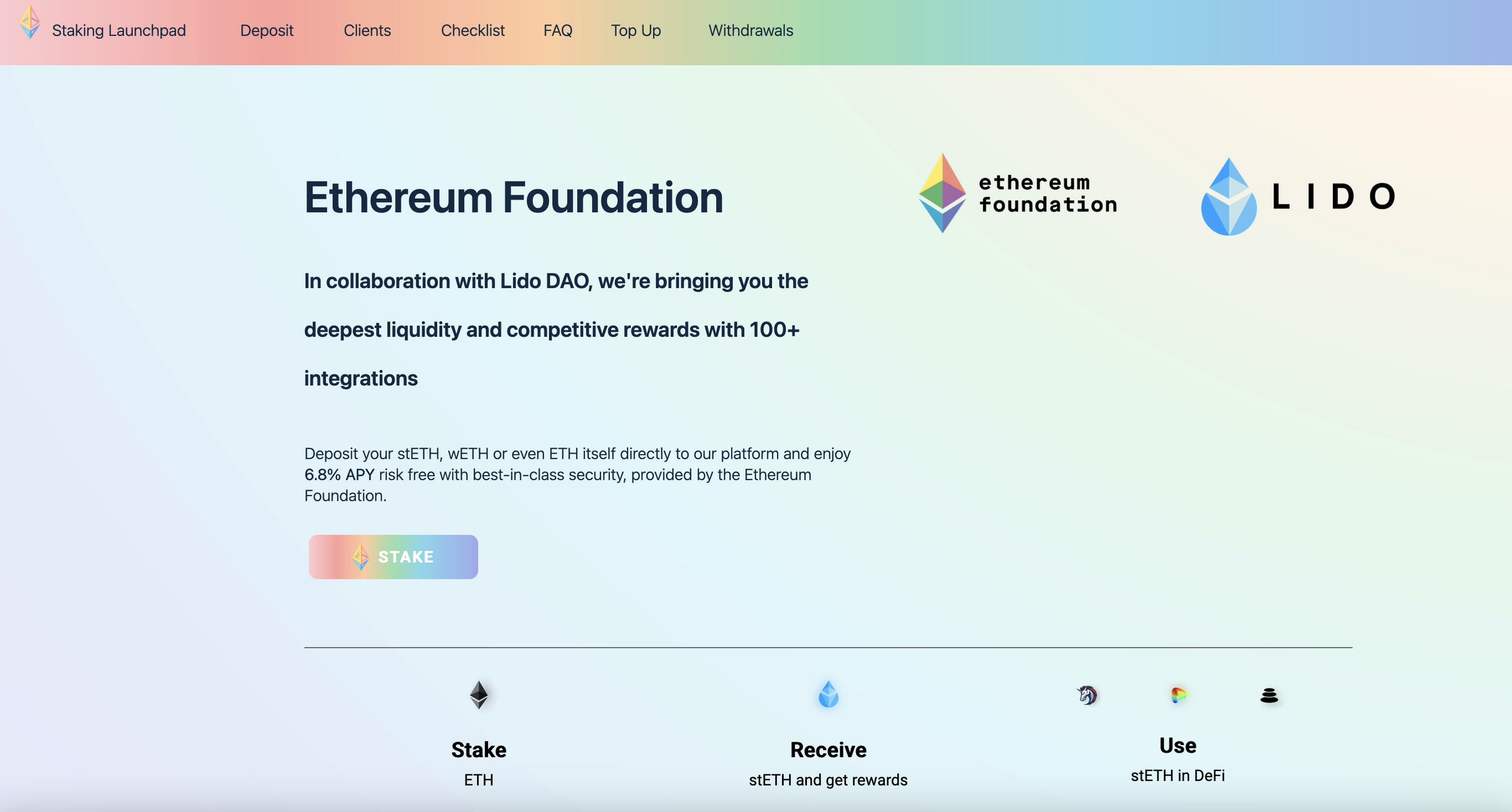
This web site had a crypto drainer operating within the background, and if a person initiated their pockets and signed the transaction requested by their web site their pockets would have been drained.
Our inside safety workforce instantly launched an investigation to assist decide who launched the assault, what the purpose of the assault was, when it occurred, who was affected, and the way it occurred.
A few of the intial actions taken have been:
- Prevented the risk actor from sending extra emails.
- Despatched out notifications through twitter and e mail to not click on the hyperlink in query.
- Closed down the malicious entry path the risk actor had used to acquire entry into the mailing listing supplier.
- Submitted the malicious hyperlink to numerous blacklists, and it was then blocked by majority of web3 pockets suppliers and cloudflare.
Our investigation into the assault confirmed that:
- The risk actor imported a big e mail listing of their very own into the mailing listing platform for use for the phishing marketing campaign.
- The risk actor exported the weblog mailing listing e mail addresses, which was a complete of 3759 e mail addresses.
- Once we in contrast the emails within the e mail listing that the risk actor had imported, we may see that the weblog mailing listing contained 81 e mail addresses that the risk actor didn’t beforehand have information of, and the remaining have been duplicate addresses.
- Analyzing on-chain transactions made to the risk actor between the time they despatched out the e-mail marketing campaign and the time the malicious area acquired blocked, seem to indicate that no victims misplaced funds throughout this particular marketing campaign despatched by the risk actor.
As we proceed engaged on this incident, we’ve got taken extra measures reminiscent of migrating some mail providers to different suppliers, to additional assist cut back the chance of this occurring once more.
We’re deeply sorry that this incident occurred, and are working diligently with each our inside safety workforce in addition to exterior safety groups to additional assist deal with and examine this incident.
Any questions will be directed to [email protected].

